Hackers are finding more ways to attack the data of companies and commit cybercrimes. Retail companies have needed to improve their security after cybercrimes caused a massive data breach in 2013 putting millions of credit and debit card holders at risk of being hacked. Since then, companies like Target have been revamping their data security so consumers private information is not stolen. Hackers are also going after people, specifically places of employment, with phishing emails that also puts a company’s information at risk. Technology is making advances where everything goes through the internet, including building controls. New building control systems relying on Bluetooth and other modes of internet can also be at risk of data breaches and cybercrimes. IT departments are looking for ways to enforce their cyber security to the new standards major companies are using to protect their information.
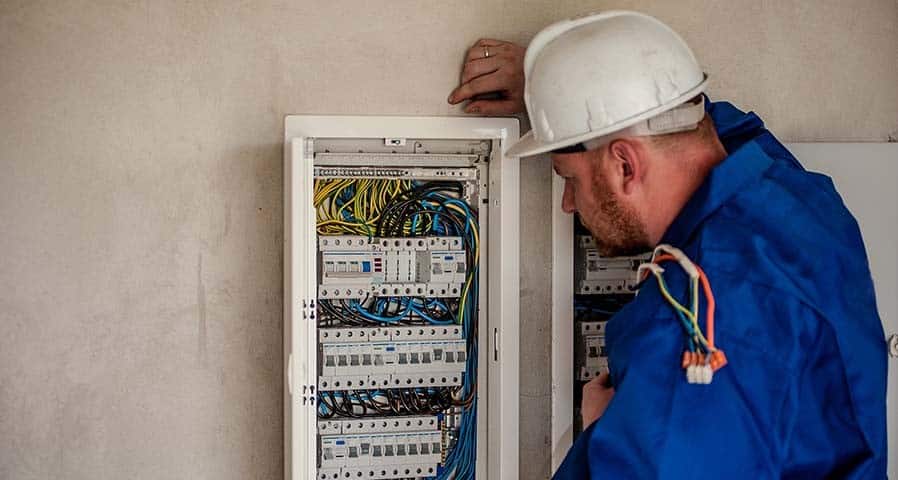
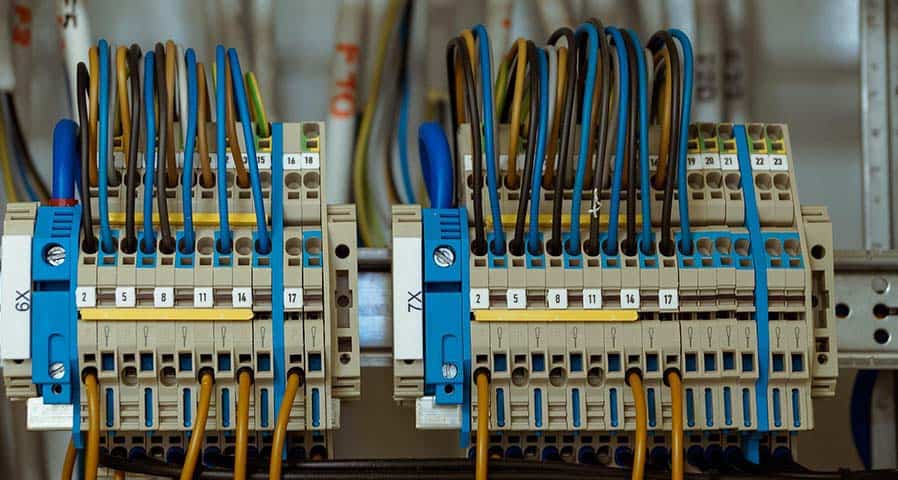
IT systems are working hard to enforce the security of their wireless connections, which includes surveillance, lighting and numerous other software that run through buildings. This can be done by connecting data through Ethernet, Bluetooth, and other wireless connectivity. IT workers identify potential weaknesses in their systems to see what needs to be reinforced. They are also trying to protect devices that are being used on the internet such as cell phones and other smart devices.
There is a bill that was passed called Internet of Things Cybersecurity Improvement Act of 2020. This act protects Internet of Things (IoT) from cybersecurity attacks. IoT are physical devices that are connected to the internet. IoT devices are at an extra risk of a cyberattack. These devices can be hacked due to unsecure devices that can get into or hack your Wi-Fi password. This can affect smart buildings because if the devices aren’t secure then hackers can cyberattack the functions of the building such as the lighting controls and security cameras. This new act of legislation is one of the first steps to ensuring the security of internet connected devices.
Click here to read the full article originally posted on LEDs Magazine.

































0 Comments